In this article, we’re going to go through how to secure android phone from being hacked.
More than billions of individuals are using android devices today.
Cybercriminals can hack your Android smartphone in different ways that you may not understand.
Android consumers, however, have also become hackers ‘ prime target. So, what can you do to keep your computer from hacking?
Table of Contents
how to secure android phone:


You can follow some very easy tips to secure your Android phone:
Keep up to date your operating system & apps
Have you been alerted to an OS or app update by your mobile-and you overlooked that notice?
Once an update is prepared for Android or Apple, download it and install it. Many hackers take advantage of outdated OS vulnerabilities.
A new update to Android always comes with some fresh function and bug fixing that might happen in past releases. The purpose of these updates is to keep your phone’s correct functioning and provide the greatest possible safety.
So install it immediately the next time you see an update, message, software.
Do not save your passwords in your browser


We trend to save internet services and websites our passwords.
Have you ever thought, however, that if any hacker had your phone in his hands then he could access all the accounts with the help of saved passwords? So make sure you don’t save in internet equipment and websites all your important passwords.
Also Read: Secure Your browserBe careful about downloading apps
Make sure it’s secure and legit before you download an app from the Google Play Store. Some apps created by hackers slide through the cracks.
Be sure to verify the name of the developer and the reviews of other customers when downloading applications. If there’s something wrong, prevent downloading the app you’re looking at.
How to Detect Google Play Store Fack Apps:
1. Be careful about the name and company
Two applications can not have the same name. In some ways, a copycat app has to be distinct from the original. Check each app’s name closely as you’ll discover the details somewhere: an additional or missing letter, a logo in a different color, a spelling mistake that changes everything, etc.
2.Comments and Ratings
Comments and ratings are the tall sign telling keys. If you see very tiny ratings and comments that highlight “this is a fake app,” we recommend you be cautious.
Avoid login automatically
It may seem convenient to you, but it makes it as simple as your browser to operate. Take the moment to enter your usernames and passwords, especially on banking and other sensitive websites of the business.
Connect only to secure Wi-Fi networks
Wi-Fi is one entry-point hacker that can be used to get into your network without setting foot inside your building because wireless is much more accessible to eavesdroppers than wired networks, which implies that you need to be more careful about safety.
Only use secure Wi-Fi networks when you’re out in the public. Better yet, use a private mobile hotspot of your own! Public Wi-Fi is the simplest way for hackers to access their Android phone.
It is known that hackers create fake, realistic-looking networks of government to attract victims. When someone connects to one of these fake Wi-Fi connections, the hacker then steals their smartphone information.
Keep in mind that free Wi-Fi can cost you a lot as hackers can readily bypass all securities via this Wi-Fi and hack your Android and access your private information.
install security software
Don’t download just any app. Read recommendations from trustworthy sources like Consumer Reports (Consumer Reports link).
go with Avast, which offers safety and malware protection, if you want free, reliable protection. if you’re prepared to pay extra for protection against heavy-duty. go to McAfee.
set a passcode
Sure, keeping your phone open all the time is much easier because you can get faster to your email, texts, camera, and other characteristics.
But just believe about how you’d feel if a stranger discovered your mobile on a bus seat or in a coffee shop and just click on your email or contacts or banking app or pictures.
Always engage the four- or six-digit passcode to prevent this from happening. So if you ever lose track of your phone, it won’t open up a stranger to your entire business.
Choose something complicated yet simple to remember. Evite bank PINs, birthdays, or any portion of your phone number.
Delete history of the browser / cache on a regular basis
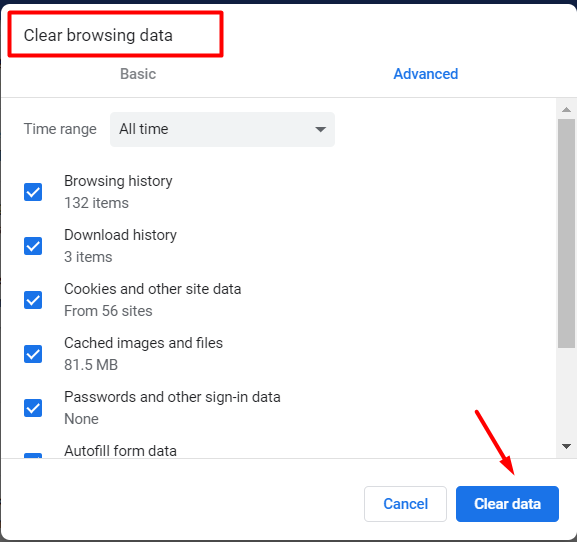
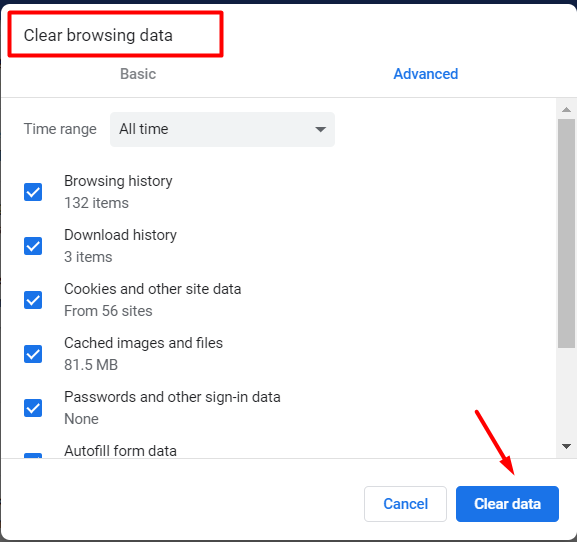
History and cache can store cookies that may contain your private login information, so it’s better to frequently remove them.
use two-factor authentication
You add an extra layer of security to your account with a 2-step verification (also known as two-factor authentication).
Two-step verification is a technique involving two methods of authentication performed one after the other to verify who or what they are declared to be someone or something seeking access.
Well, if you use a PIN, password, or fingerprint protection to lock your Android device, let’s lock your google service as well.
Google has its own two-factor authentication to enhance your Android security. By switching on two-factor authentication, anyone trying to hack your accounts will need the security codes sent to your registered phone number.
[All major websites and applications now support authentication with two factors.]
Use Google Find My Device
Well, finding my device is the service Google provides and it helps customers find their phone when theft occurs.
If you have recently lost your phone and it ends up in hackers ‘ hands, they can do more damage than you can imagine.
So, the best way to use Google’s Find my device service is to help clients lock the phone when they feel the need.
So these are all techniques to keep your Android from hacking.
Hope you like the post. Don’t forget to share it.
